Security labelling
As with the inode security label, AppCL LSM allocates a file security label. This is done using the ‘file_alloc_security’ and ‘file_free_security’ hooks.
Attributes of these security labels are now permission flags and masks as defined by ‘richacl’, as used with extended access control. These attributes are still to be properly defined by AppCL. Sample values are used at present.
file_open hook
The file_open hook is now initialised as shown below. This hook is accessed whenever a new filesystem object is opened.

Currently AppCL retrieves the file security label and inode security label for the open file system object. It then goes on to identify the path name of that object (fpath_name).
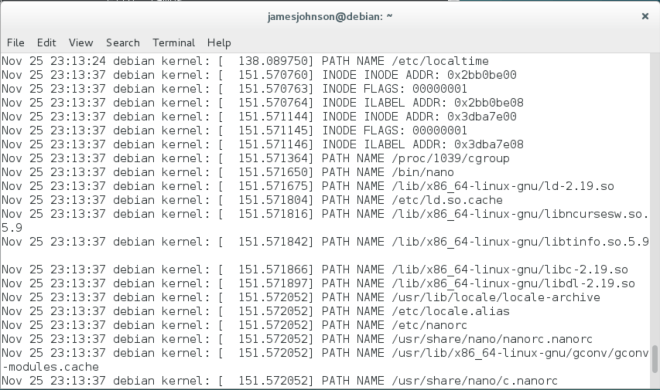
The screenshot below shows the output from the kernel log when running ‘nano’. The pathname for every file object opened by the nano application is then printed.
To manage the process of loading new programs AppCL LSM will use the LSM program loading hooks (binprm).
To view the public git for this project visit:
